Bypassing HttpOnly with phpinfo file
Before I start explaining how we were able to bypass the HttpOnly flag, let's discuss what HttpOnly even is:
HttpOnly is an additional flag included in a Set-Cookie HTTP response header. Using the HttpOnly flag when generating a cookie helps mitigate the risk of the client-side script accessing the protected cookie, If the HttpOnly flag (optional) is included in the HTTP response header, the cookie cannot be accessed through a client-side script, if the browser supports this flag. As a result, even if a cross-site scripting (XSS) flaw exists, and a user accidentally accesses a link that exploits this flaw, the browser will not reveal the cookie to a third party.
If a browser does not support HttpOnly and a website attempts to set an HttpOnly cookie, the HttpOnly flag will be ignored by the browser, thus creating a traditional, script accessible cookie. As a result, the cookie (typically your session cookie) becomes vulnerable to theft of modification by malicious script. — source
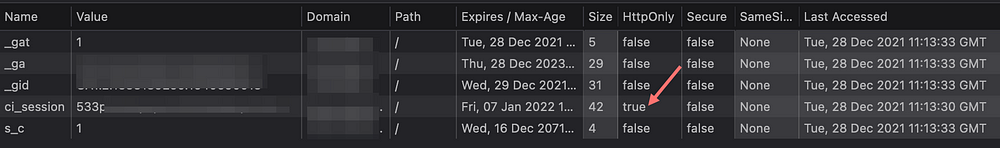
While doing Web Application assessment with Higgsx, We found stored Cross-Site Scripting(XSS) which was a nice finding but we could not escalate it any further because of the HttpOnly flag on the session cookie - ci_session:
There are a few well-known ways to Bypass the HttpOnly flag:
- Stealing it if the target accepts TRACE Method, in that case, the TRACE method was enabled, but modern web browsers no longer support it by default, so exploiting it with the TRACE method was pointless.
- Getting the HttpOnly cookie from the response, which does not work for us — https://www.shorebreaksecurity.com/blog/xss-exploitation-with-xhr-response-chaining/
And after struggling for a few hours, we got a new idea...
so, why phpinfo?
Almost every website, which I am testing,(of course, based on PHP) has phpinfo file.
If you going to report them in a bug bounty program, you won’t get a bug bounty by only finding phpinfo, because the impact in most case scenarios is very low.
After some directory and file enumeration, we came across the info.php file:

The most interesting part of the phpinfo, is that it reads every cookie, even HttpOnly ones.

Stealing ci_session with info.php file
We found XSS in a name field, now we can abuse the XSS to load our JavaScript, which using XMLHttpRequest() reads info.php and sends it
We created this JS code that reads the info.php, gets the value “HTTP_COOKIE” and sends it back to our server.
info.js file:
After creating the JavaScript file, we can inject the Payload in the last name field(it was vulnerable to our case):

Here is our request, containing info.php content(in base64)

And by simple decoding the base64 data, we can see that ci_session

After getting the ci_session, we got access to the administrator account and escalated our privileges from the user.
P.S. The JavaScript can be improved much more, feel free to contribute
P.S.2 Tomcat has examples that can be used same way
/examples/servlets/servlet/SessionExample